Traceability Matrix from Software Testing perspective
Traceability Matrix is used in entire software development life cycle phases:
- Risk Analysis phase
- Requirements Analysis and Specification phase
- Design Analysis and Specification phase
- Source Code Analysis, Unit Testing & Integration Testing phase
- Validation – System Testing, Functional Testing phase
In this topic we will discuss:
- What is Traceability Matrix from Software Testing perspective? (Point 5)
- Types of Traceability Matrix
- Disadvantages of not using Traceability Matrix
- Benefits of using Traceability Matrix in testing
- Step by step process of creating an effective Traceability Matrix from requirements. Sample formats of Traceability Matrix basic version to advanced version.
In Simple words – A requirements traceability matrix is a document that traces and maps user requirements [requirement Ids from requirement specification document] with the test case ids. Purpose is to make sure that all the requirements are covered in test cases so that while testing no functionality can be missed.
This document is prepared to make the clients satisfy that the coverage done is complete as end to end, this document consists of Requirement/Base line doc Ref No., Test case/Condition, and Defects/Bug id. Using this document the person can track the Requirement based on the Defect id
Note – We can make it a “Test case Coverage checklist” document by adding few more columns. We will discuss in later posts
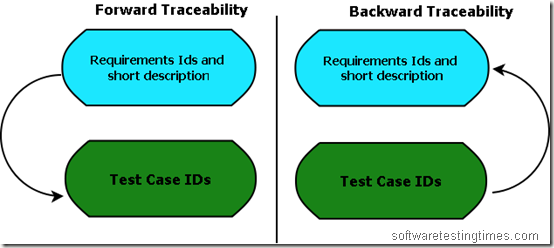
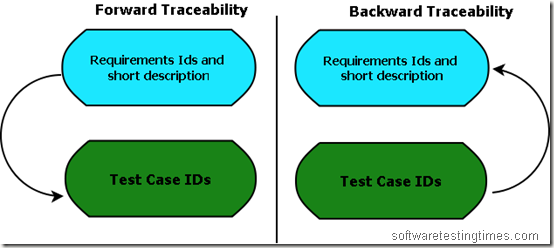
Types of Traceability Matrix:
- Forward Traceability – Mapping of Requirements to Test cases
- Backward Traceability – Mapping of Test Cases to Requirements
- Bi-Directional Traceability – A Good Traceability matrix is the References from test cases to basis documentation and vice versa.
Why Bi-Directional Traceability is required?
Bi-Directional Traceability contains both Forward & Backward Traceability. Through Backward Traceability Matrix, we can see that test cases are mapped with which requirements.
This will help us in identifying if there are test cases that do not trace to any coverage item— in which case the test case is not required and should be removed (or maybe a specification like a requirement or two should be added!). This “backward” Traceability is also very helpful if you want to identify that a particular test case is covering how many requirements?
Through Forward Traceability – we can check that requirements are covered in which test cases? Whether is the requirements are coved in the test cases or not?
Forward Traceability Matrix ensures – We are building the Right Product.
Backward Traceability Matrix ensures – We the Building the Product Right.
Traceability matrix is the answer of the following questions of any Software Project:
- How is it feasible to ensure, for each phase of the SDLC, that I have correctly accounted for all the customer’s needs?
- How can I certify that the final software product meets the customer’s needs? Now we can only make sure requirements are captured in the test cases by traceability matrix.
Disadvantages of not using Traceability Matrix [some possible (seen) impact]:
No traceability or Incomplete Traceability Results into:
1. Poor or unknown test coverage, more defects found in production
2. It will lead to miss some bugs in earlier test cycles which may arise in later test cycles. Then a lot of discussions arguments with other teams and managers before release.
3. Difficult project planning and tracking, misunderstandings between different teams over project dependencies, delays, etc
Benefits of using Traceability Matrix
- Make obvious to the client that the software is being developed as per the requirements.
- To make sure that all requirements included in the test cases
- To make sure that developers are not creating features that no one has requested
- Easy to identify the missing functionalities.
- If there is a change request for a requirement, then we can easily find out which test cases need to update.
- The completed system may have “Extra” functionality that may have not been specified in the design specification, resulting in wastage of manpower, time and effort.
Steps to create Traceability Martix:
1. Make use of excel to create Traceability Matrix:
2. Define following columns:
Base Specification/Requirement ID (If any)
Requirement ID
Requirement description
TC 001
TC 002
TC 003.. So on.
3. Identify all the testable requirements in granular level from requirement document. Typical requirements you need to capture are as follows:
Used cases (all the flows are captured)
Error Messages
Business rules
Functional rules
SRS
FRS
So on…
4. Identity all the test scenarios and test flows.
5. Map Requirement IDs to the test cases. Assume (as per below table), Test case “TC 001” is your one flow/scenario. Now in this scenario, Requirements SR-1.1 and SR-1.2 are covered. So mark “x” for these requirements.
Now from below table you can conclude –
Requirement SR-1.1 is covered in TC 001
Requirement SR-1.2 is covered in TC 001
Requirement SR-1.5 is covered in TC 001, TC 003 [Now it is easy to identify, which test cases need to be updated if there is any change request].
TC 001 Covers SR-1.1, SR, 1.2 [we can easily identify that test cases covers which requirements].
TC 002 covers SR-1.3.. So on..
| Requirement ID | Requirement description | TC 001 | TC 002 | TC 003 |
| SR-1.1 | User should be able to do this | x | ||
| SR-1.2 | User should be able to do that | x | ||
| SR-1.3 | On clicking this, following message should appear | x | ||
| SR-1.4 | x | |||
| SR-1.5 | x | x | ||
| SR-1.6 | x | |||
| SR-1.7 | x |
This is a very basic traceability matrix format. You can add more following columns and make it more effective:
ID, Assoc ID, Technical Assumption(s) and/or Customer Need(s), Functional Requirement, Status, Architectural/Design Document, Technical Specification, System Component(s), Software Module(s), Test Case Number, Tested In, Implemented In, Verification, Additional Comments,
Click here to download sample advanced version of traceability matrix.

Recent Comments